I’m now running a Pi-hole on my home network. What is it? The docs describe it as “a DNS sinkhole that protects your devices from unwanted content, without installing any client-side software.”
You get it running on your network, and then you configure your router to ask it for how to translate hostnames (like www.example.com) into IP numbers (like 10.53.48.102), which is how computers look each other up on the internet, instead of asking your internet service provider or Google. Pi-hole does the talking to your provider to look up the numbers where it needs to, but if your computer or phone asks to look up a server that just runs ads, the Pi-hole gives back a wrong answer.
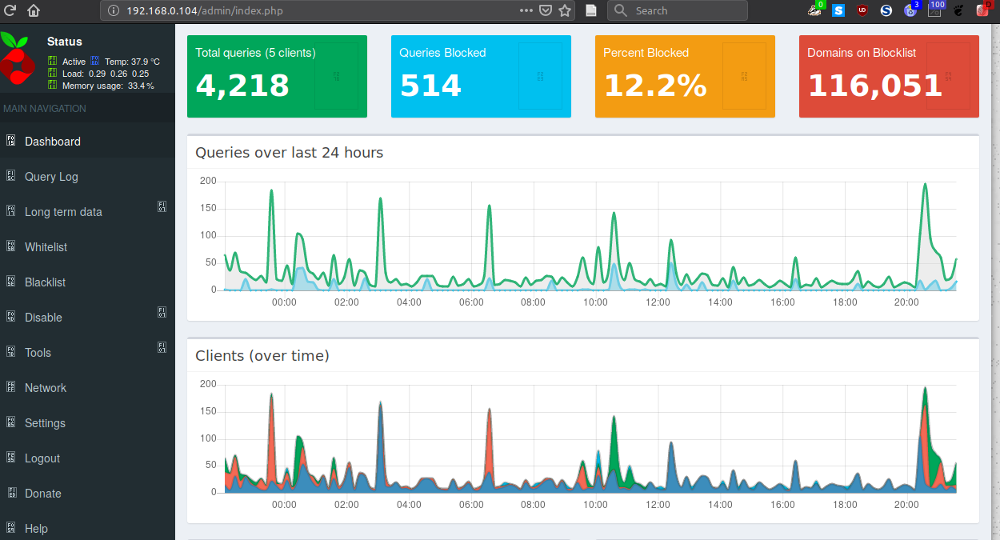
This is a screenshot of what it’s blocked recently, taken from its very nice web dashboard:

This shows pretty clearly that I run Ubuntu, my main browser is Firefox, my music streaming service is Tidal and I read the Guardian. All true. (I also have uBlock Origin and NoScript and other blockers running inside Firefox, so a lot of requests are being blocked on my laptop before any network requests are made.)
It also shows a lot of requests to Mozilla for Firefox-related stuff I probably don’t need, and I also don’t need that network connectivity check all the time. I’ll probably turn those off.
One of the blocked sites on the right is metrics.cbc.ca, which must be getting requested by the CBC News app on my phone. A DNS lookup on that hostname outside my network shows it’s available at several IP numbers (this is round-robin DNS used for load balancing on busy servers):
$ nslookup metrics.cbc.ca
Server: 208.67.222.222
Address: 208.67.222.222#53
Non-authoritative answer:
metrics.cbc.ca canonical name = cbc.ca.122.2o7.net.
Name: cbc.ca.122.2o7.net
Address: 3.208.14.195
Name: cbc.ca.122.2o7.net
Address: 3.219.244.74
Name: cbc.ca.122.2o7.net
Address: 34.234.23.242
Here’s the same request on my home network, where the answer is: nothing.
$ nslookup metrics.cbc.ca
Server: 127.0.0.53
Address: 127.0.0.53#53
Non-authoritative answer:
Name: metrics.cbc.ca
Address: 0.0.0.0
Name: metrics.cbc.ca
Address: ::
That’s why I don’t see any ads in the CBC News app when I’m on my home wifi.
Here’s the top of the dashboard, where it shows activity:
I am running this on a Raspberry Pi Zero W, which is a tiny computer. It’s the small thing with the glowing green light, beside my Presto card (the size of a credit or debit card) for scale. It cost about $25 at Creatron in downtown Toronto. (The slightly larger thing is a Raspberry Pi Four, on which I’m running a Tor relay.)

Setting up Pi-hole is nontrivial. You need to get the operating system onto an SD card, plug in a keyboard and monitor long enough so you can boot it up and configure it to get it on the network, then install Pi-hole at the command line, then reconfigure the DNS settings on your router so it talks to the Pi-hole. If you’ve never used the command line or changed settings on your router, that’s not something you want to tackle lightly.
But, if you’ve ever done those two things, setting up a Pi-hole is remarkably simpler than you might expect. You might be scared you’ll mess up your whole network, but (as long you write down your original router settings) it’s easy to back out if something goes wrong—but the Pi-hole people have done such a great job it probably won’t. It got it all working in about thirty minutes, start to finish. (Once I actually had all the cables and stuff so I could attach a keyboard and monitor.)
I’m so impressed I got another Pi Zero W and I’m going to set up a Pi-hole at someone else’s house—someone who doesn’t run as many ad blockers in their browsers as I do, so I think they’ll see much more improvement than I did. After that I may do more people. Installing a Pi-hole seems like an easy way to magically improve everyone’s internet experience without them having to do anything.
 Miskatonic University Press
Miskatonic University Press